Security audit & risk assessment
Threat modeling, asset inventory, gap analysis, maturity mapping, and a 90/180-day roadmap.
output: scope, risk register, implementation plan3nd security is a cybersecurity integrator that starts from the end: from impact scenarios and critical attack chains — to architecture, implementation, and operational security.
Engineering, architecture, and operations — vendor-agnostic, with measurable quality metrics.
Threat modeling, asset inventory, gap analysis, maturity mapping, and a 90/180-day roadmap.
output: scope, risk register, implementation planEDR/XDR, SIEM, NDR, WAF, PAM, SSO/MFA, vulnerability management, hardening, and configuration control.
output: architecture, runbooks, operational handoverUse cases, normalization, correlation, quality metrics, SOAR steps, and source onboarding.
goal: fewer blind spotsIAM hardening, segmentation, CSPM/CWPP approach, secrets, logging, and monitoring.
goal: exposure controlWeb/API, infrastructure, AD, cloud. Reports with PoCs and prioritized remediation.
output: reproducible findings & fixesPlaybooks, tabletop exercises, forensics, incident support, recovery, and lessons learned.
goal: reduce downtimeSecurity documentation, access governance, vendor risk, BCP/DRP, and audit preparation.
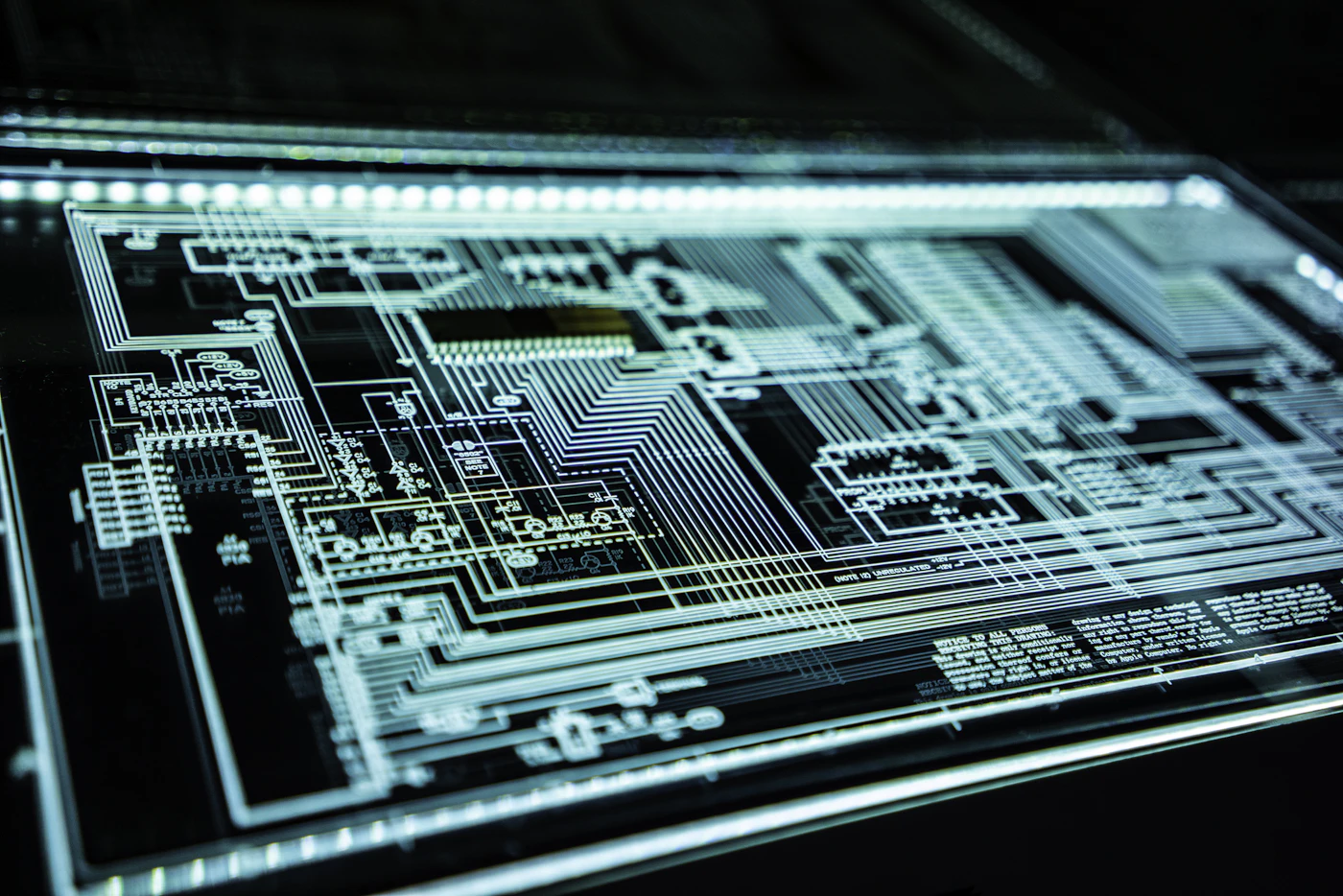
approach: pragmatics over paperwork“What we did → what changed.” Stock images with monochrome grading.


Start with impact and attack chains. Then build controlled architecture and operations.
Define what must not happen: downtime, breach, compromise, fines, reputational damage. Set criticality.
Assets, paths, dependencies, vendors, remote access, cloud. Build a prioritized risk map.
Select controls and processes: IAM, endpoint, network, email, backups, monitoring. Do less, but do it right.
Metrics, checks, exercises, and retests: prove the defense works in real scenarios.
Placeholders — replace with real references (no names/logos used here).
We built a risk map and a roadmap, then implemented monitoring and baseline playbooks — fewer blind spots and clearer KPIs.
The pen test delivered clear PoCs and priorities. The team helped fix critical issues and validate remediation.
We improved access governance and segmentation. “From the end” kept the scope focused on what mattered most.